Overview of Our Network Penetration Services
Closing All Doors Before the Bad Guys Come In!
Bad guys are always looking for easy target! They have powerful tools in their hands. Anonymity coupled with a strong monetary incentive to break in your systems and steal valuable data provides a great motivation.
Security vulnerabilities, such as weak configurations, un-patched systems, and botched architectures, continue to plague organizations. Enterprises need people who can find these flaws in a professional manner to help eradicate them from our infrastructures.
Lots of people claim to have penetration testing, ethical hacking, and security assessment skills, but precious few can apply these skills in a methodical regimen of professional testing to help make an organization more secure. Our experts at Rapidsoft Systems are trained to use the latest penetration testing tools.
What Can You Expect From Our Testing
Our experts perform detailed pre-test planning, including setting up an effective penetration testing infrastructure and establishing ground rules with the target organization to avoid surprises and misunderstanding. Then, we utilize a time-tested methodology for penetration and ethical hacking across the network, evaluating the security of network services and the operating systems behind them.
An expert at Rapidsoft Systems can answer all the above questions and help your company assess your risks and create an effective policy for your organization.
Rapidsoft Systems' Network Penetration Testing Services
Network penetration testing (aka pen testing) and timely identification of network vulnerabilities is something that you simply cannot ignore in today's vulnerable networks. Every organization needs to close its weak doors and amend its weak links before hackers or disgruntled insiders exploit the weaknesses. The process of identifying vulnerabilities, evaluating the risk, remediation, and reporting is called vulnerability management. By running penetration tests, organizations are able to more efficiently find and fix security vulnerabilities within their network.
Automated pen testing techniques can help you in detecting potential attack paths, and making changes. These changes often need to encompass both technology and business process changes. The good news that the use of modern powerful tools can do deep inspection of your code, your firewalls, your policies and your devices. A typical penetration tool can run thousands of tests and create very detailed reports for risks within your systems.
Standard penetration testing is a method of probing and identifying security vulnerabilities in your network and the extent to which they could be exploited by a hacker. These tests are typically performed using automated tools that look for specific weaknesses, technical flaws or vulnerabilities to exploit, with the results presented to the system owner with an assessment of their risk to the networked environment and a remediation plan highlighting the steps needed to eliminate the exposures.
Our Penetration Testing Tools
The Nessus® vulnerability scanner, is the world-leader in active scanners, featuring high speed discovery, configuration auditing, asset profiling, sensitive data discovery and vulnerability analysis of your security posture. Nessus scanners can be distributed throughout an entire enterprise, inside DMZs, and across physically separate networks.
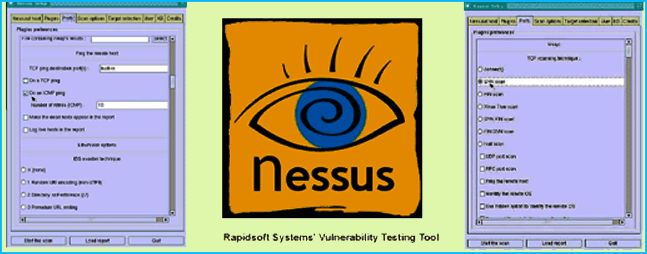
Nessus - One of Many Tools For Network Vulnerability Testing
Vulnerability management and penetration testing work hand in hand to close any potential openings available to corporate attackers. Together, vulnerability management and penetration testing enhance security and lessen the probability that the criminals could penetrate your systems.
Penetration Testing Methodology
To provide the most comprehensive vulnerability assessment results possible, our consultants work closely with your organization to clearly define the network components to be assessed. Often, this includes assessing the security of:
- File Servers
- Database Servers
- Custom Applications
- Web Servers - Apache, IIS
- Mobile Devices and Applications Servers
- Email Servers
- Employee Workstations
- Application Servers
- Routers and Switches
- Storage Area Networks
- Commercial Off The Shelf Software
- Firewalls
Network Vulnerability Testing in Progress
Application Testing For Security Vulnerability
We use various special purpose tools including code and attack verifications to identify any vulnerability in the applications developed on your system. Our team of speciliasts will attempt to exploit each system with a variety of techniques including, among others:
- Input validation
- SQL injection
- Buffer overflow
- Hidden variable manipulation
- Cross-site scripting
- Cookie modification
- URL manipulation
Rapidsoft Systems security consulting services team can plan, design, perform industry standard penetration tests to your network. Our team will provide a report of the results along with the risk assessment report. We have the resources to test your network perimeter using our external server based Scanning Engines.
How do I get started?
To learn more about how a TotalCare 360® IT managed services plan can help support and grow your business, please call 1-609-439-4775 and / or fill out our contact form. You can be sure that a member of our managed IT services consulting teams will be happy to assist you.